Operation Blackout
By Simvado
A coordinated cyberattack cripples a major financial institution. As the CISO, you must lead the incident response team through containment, forensic analysis, stakeholder communication, and recovery — all while the clock ticks and attackers probe deeper into the network.
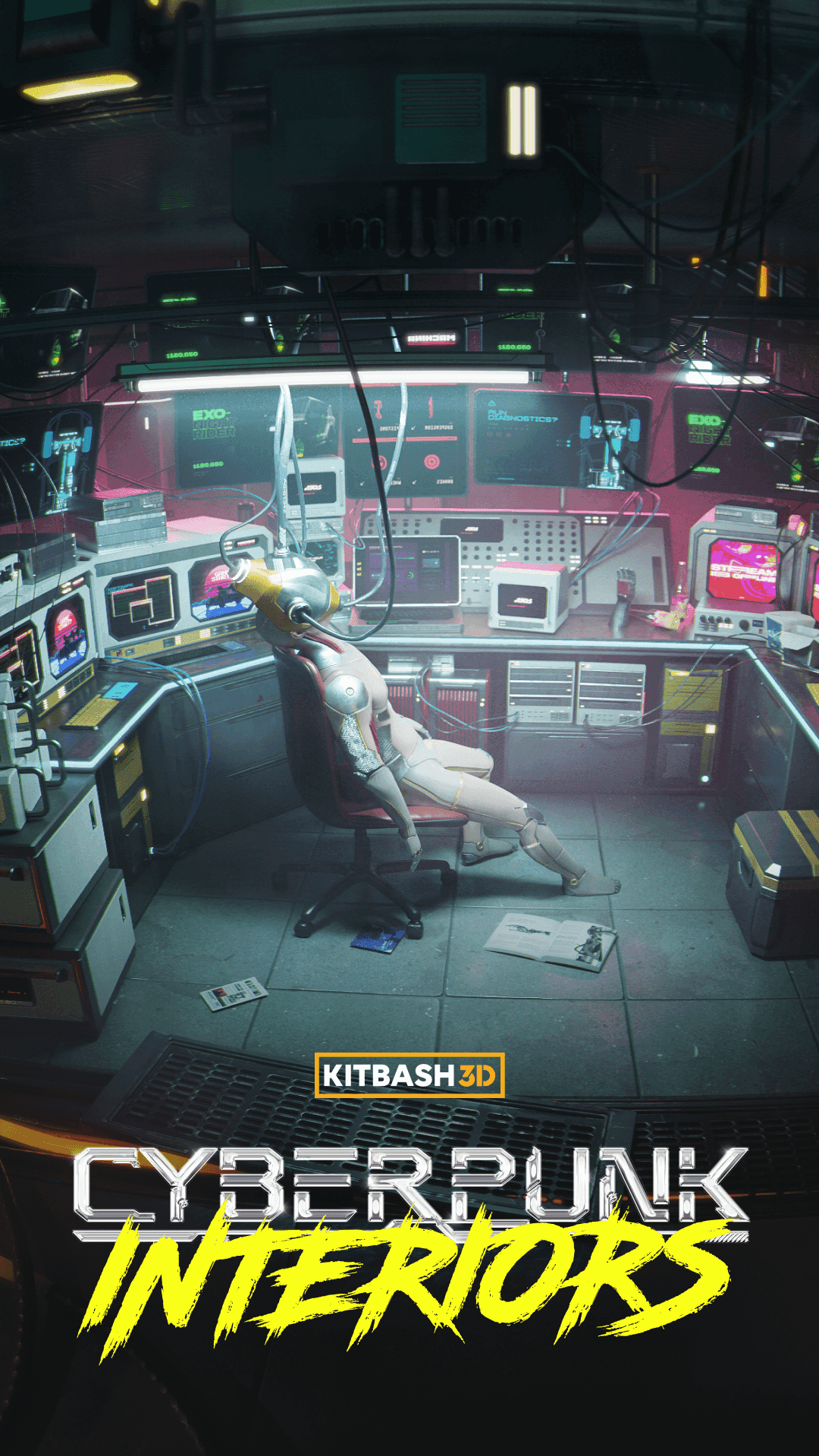
Environment Gallery



Scenario Overview
It is 2:47 AM when your phone rings. The Security Operations Center has detected anomalous network traffic patterns across your bank’s core transaction processing systems. Within minutes, automated alerts cascade across every monitoring dashboard — someone is inside the network, and they are moving fast. As the Chief Information Security Officer of Meridian National Bank, you are the last line of defense for 28 million customer accounts and $340 billion in assets.
The attackers are sophisticated. They have bypassed perimeter defenses using compromised vendor credentials and are now executing lateral movement across the network, targeting the SWIFT transaction gateway and customer identity databases simultaneously. Your SOC team is overwhelmed, the board chair is calling, and a financial regulator has already been tipped off by unusual transaction patterns. Every decision you make in the next ninety minutes will determine whether this becomes a contained incident or a front-page catastrophe.
You must assemble your crisis team, isolate compromised systems without shutting down critical banking operations, manage communications across a dozen stakeholder groups, and ultimately lead the recovery — all while the attackers adapt their tactics in real time. This is not a drill. The institution’s reputation, your customers’ trust, and potentially the stability of the broader financial system hang in the balance.
Skills Developed
Learning Objectives
- 1Lead an incident response team through a coordinated, multi-vector cyberattack on critical financial infrastructure
- 2Communicate effectively with regulators, board members, and the media under extreme time pressure
- 3Apply forensic decision-making to identify attack vectors and prioritize containment actions
- 4Coordinate cross-functional teams spanning security operations, legal, communications, and executive leadership
- 5Conduct a rigorous post-mortem analysis and translate findings into actionable remediation plans
Scoring Dimensions
Every decision you make is scored across five leadership dimensions.
Modules (4)
Initial Detection
Free Demo20 min
Anomalous network traffic is detected at 2:47 AM. Your SOC team escalates to you. Assess the situation and activate the incident response plan.
Containment Protocol
25 min
The breach is spreading through lateral movement. Isolate compromised systems without disrupting critical banking operations.
Stakeholder Communication
20 min
Regulators, the board, customers, and the media are demanding answers. Craft your communications strategy while managing legal exposure.
Recovery & Post-Mortem
25 min
Restore operations and lead the post-incident review. Identify root causes, remediation steps, and present to the executive committee.
Ready to start training?
Create a free account to play your first simulation module. Upgrade to Pro for unlimited access to every scenario in the library.